
Figure 1: The distribution of data breaches from 2021 to 2023 across different industries [2]
There are many examples of these high-profile financial security breaches happening in recent times. For example, a London-based fintech firm, Finastra, recently confirmed a heavy data breach that resulted in the theft of approximately 400 gigabytes of compressed information [3].
In 2017, Equifax, a US-based credit reporting agency failed to update their servers with a security patch after being alerted to it. This exposed the information of approximately 147 million people resulting in about $425 million in fines [4].
Another example is that of Flagstar Bank, which suffered a massive data breach in 2022 that led to the leaking of Social Security Numbers of almost 1.5 million customers [5].
Again, cybercriminals using fintech applications can also launder money via crypto. One recent report revealed that $22 billion was laundered via crypto platforms in 2023 alone [6].
We can go on and on with similar scenarios. But make no mistake about it, the key takeaway here is that they only go to reveal the magnitude of security risks that surround most fintech applications, and the reasons why developers need to prioritize consumer trust, safety, and regulatory compliance in their app development.
As with every industry where personally identifiable information (PII) is handled on a large scale, it’s common for fintechs to be targeted in cyber attacks.
With the scale of PII handled by fintech apps, it comes as no surprise that they face many challenges in protecting sensitive user data running on their applications.The evolving nature of fintech cyber threats means that preventing these breaches is getting tougher by the day.
A study by financial services research firm Javelin highlights the severity of the issue, revealing that identity fraud alone resulted in $23 billion in losses in 2022 [7]. Other frauds like phishing scams, credential stuffing, and advanced persistent threats (APTs) are also becoming a major concern and difficult to contain.
Another challenge in fintech applications is centered around penalties resulting from non-compliance to regulatory standards.
Fintechs are required to adhere to stringent laws like the General Data Protection Regulation (GDPR), Payment Card Industry Data Security Standard (PCI DSS), and anti-money laundering regulations. Most start-up firms in finance often grapple with maintaining up-to-date audit trails which can lead to hefty penalties.
The need to stay ahead of evolving attack vectors while staying compliant often forces fintechs to juggle operational complexity and rapidly shifting regulatory landscapes.
According to the United States Government Financial Modernization Act of 1999 [8], financial institutions are mandated to protect the privacy of consumers’ finances and data.
The same is also applicable to other top countries like the UK, where the Data Protection Act 2018 [9] controls how organizations including fintechs use customers' personal information. So, it is no surprise that many fintechs are now taking data protection very seriously.
For instance, the PCI DSS is a vital framework for fintechs that handle credit card information. Most fintechs are also bound to adhere to regulatory requirements, such as the GDPR in Europe and the California Consumer Privacy Act (CCPA) in the United States.
Figure 2: The scope of PCI DSS and GDPR [10]
Below are a few ways I suggest fintechs can protect customer financial data whilst remaining compliant with the industry standards.
Encryption is very important in ensuring data integrity and confidentiality. As a fintech firm, integrating advanced encryption protocols in app development will reduce the likelihood of data breaches.
For instance, if you're a fintech firm trying to secure your customers' credit card numbers, I advise you to build an application that encrypts data before storage. If you're coding with Python, the cryptography library can be used to implement the encryption standard. In this case, I usually use AES encryption which is very secure.
Take a look at the code below to understand how you can initiate the process.
|
from |
You can also decrypt the data during transactions or audit records by following the coding example below.
|
def decrypt_data(encrypted_data, key): |
Even If the data is breached, the attacker will only see an encrypted data like this below:
|
User_data |
Encrypted_Card_Data |
|
1 |
b’\x8b\xf4…\xaf’ |
The key point here is to make sure as a developer, that you use a strong key management system (KMS). I use AWS KMS or HashiCorp Vault in most cases to secure encryption keys for my clients. Also, rotate the keys periodically to enhance the security.
For example, at our company, we use HTTPS/TLS to encrypt data during transmission between the client, server, and database, and this is a good approach to ensure the security of data at rest and in transit.
Figure 3: How cryptographic key works in data encryption [11]
Modern fintech apps are better protected with authentication mechanisms during user verification. Strong authentication methods like MFA provide a multi-layered defense to confirm user identities before access is given.
These layers, commonly referred to as authentication factors, may include something you possess (such as a mobile device or security token), something inherent to you (like biometric data such as fingerprints or facial features), your physical location, or your behavioral patterns.
I advise developers to leverage open libraries for MFA, such as PyOTP for backend TOTP generation and Google Authenticator for client-side. Take a look at this example code below to have a grasp of how the backend setup in Python will look like:
|
from flask import Flask, request, jsonify |
On the client side, you can configure the registration so that users can scan a QR code generated from the server's secret key or they can input their password and the TOTP from their authenticator app during login. Below is an example code for that function:
|
|
With MFA embedded in apps, it becomes more difficult for threat actors to gain access to sensitive systems or individual data.
I noticed that this simplified MFA setup through QR codes and familiar tools (authenticator apps) has more user adoption, since most clients I have worked with prefer the model.
Figure 4: MFA Conceptual Model [12]
Masking and tokenization are two other variables that I encourage fintech app developers to employ to protect financial data.
Data masking works by transforming sensitive data into an obscured or fictionalized version during transactions. Depending on your intent, you can set up static masking or dynamic masking. Both ensure that real data, such as customers' PII remains secure while supporting operational needs.
While working on a mobile app that requires credit card info, I will usually mask most of the credit card details so that only the last four digits will show as illustrated in the example code below.
|
def mask_card(card_number): |
Meanwhile, tokenization works by replacing critical data with unique, non-sensitive tokens. These tokens have no intrinsic value or meaning and cannot be reverse-engineered without access to the secure tokenization system.
|
import uuid |
From the example above, you can see that the token is mapped securely to the original data in an encrypted database for retrieval only when necessary.
Due to constant changes in technology and the increase in the frequency of online transactions, most fintech start-ups are not always fully equipped to prevent fraud when they arise.
Emerging cyber threats like deepfakes, synthetic identities, and other AI-powered scams present significant challenges to these companies. Below are some new technologies I use and recommend to developers to tackle financial fraud.
I recommend incorporating AI/ML tools in fraud detection systems due to their effectiveness. Machine learning algorithms can identify phishing patterns, suspicious links, or even automated scam messages using natural language processing (NLP) and behavioral cues.
Another advantage is that predictive AI models can assess risk scores in crypto transactions, and then provide fraud alerts once an anomaly or unusual pattern is detected. Most of the AI models that my company has developed are trained on historical data so that it can label transactions that meet certain criteria as legitimate and some others as illegitimate.
For example, if a user who typically makes small, regular purchases suddenly turns around to make a large withdrawal to a foreign account, this could be flagged as an anomaly by the model.
Again, based on the data input and the model’s predictions, each transaction or activity could be assigned a risk score. What this means is that transactions with scores above a certain threshold could be flagged for human review.
Developers can also leverage blockchain technology in addition to the AI and ML tools. Blockchain provides a clear and immutable audit trail that simplifies compliance with anti-fraud regulations like KYC (Know Your Customer) and AML (Anti-Money Laundering).
Immutable records on blockchain also ensure that financial firms have a verifiable identity management system to prevent identity forgery.
I believe by building all these fraud-prevention features directly into the app architecture, businesses are better positioned to stand against advanced threats while maintaining user trust.
Mobile payments, while efficient, introduce several attack surfaces that can be exploited by threat actors. From my experience, most vulnerabilities in mobile payment systems today can be traced down to the device level. Malware infections and the use of rooted or jailbroken devices can compromise sensitive data when they bypass built-in protections.
Another risk in mobile payment is in the network transmission channel itself. When there is leakage or vulnerability during data transmission, it can expose payment data to interception risks if not corrected quickly.
These risk factors remain a primary challenge to fintech app developers, but how can they be tackled?
While various solutions exist, I recommend secure SDKs and APIs for their effectiveness in guaranteeing mobile payment security.
These solutions are designed to enforce strong encryption and authentication protocols for payment apps. They ensure that all important data is encrypted using industry-standard protocols like Transport Layer Security (TLS).
Many secure SDKs and APIs are also pre-certified for compliance, so mobile payment systems can remain compliant with regulatory requirements with minimal effort.
Implementing SDK and API is simple in just 3 steps:
The first phase is to analyze the client's existing architecture and vulnerabilities so that proper SDK will be integrated. A custom API will also be added shortly, and the process can take up to two weeks.
The next phase is where the QA team will conduct penetration testing to identify and fix potential weaknesses. API requests will also be optimized to ensure low latency for an uninterrupted user experience.
The last stage is usually where my team deploys the solution with minimal downtime and conducts training sessions for the client's developers and security team on maintaining and scaling the new system.
Also, incorporating Secure Elements (SE) and Trusted Execution Environments (TEE) in payment apps can help isolate sensitive operations, as well as shield them from malware and tampered devices.
It is important to take your mobile payment app security issue seriously. If you can't do it yourself, it's better to outsource to the right candidates.
Crypto wallets are used to store private keys needed to access and manage cryptocurrencies. The decentralized nature of cryptocurrencies means there is no central authority to turn to for recovery when there is a security breach in those wallets.
In fact, a single lapse in security such as compromised devices or stolen private keys can result in irreversible loss of crypto funds. Bugs in smart contracts may also expose funds to exploits.
Another factor that may lead to security breaches in crypto wallets is the custodian. Custodial wallets rely on third-party security to hold private keys, and there might be compromise if the wallet custodian goes bankrupt or gets hacked.
While non-custodial wallets put users in charge, they also heighten risks if keys are mishandled.
Figure 5: Crypto scams reported to the FBI over the years
Crypto Wallet Security Measures
There are three ways in which individuals can securely store their crypto assets – hardware wallets, multi-signature wallets, and cold wallets.
Hardware wallets store private keys offline, and this makes them immune to hacking attempts or malware infections targeting online wallets. They often come with additional layers of protection, such as PIN codes and recovery phrases.
Multi-signature (multisig wallets) require multiple private keys to authorize a transaction. They are more popular in joint accounts and organizational treasuries, where they ensure consensus-based asset management.
Then there are Cold wallets, which are basically any cryptocurrency storage solution that remains completely offline. Cold wallets are nearly impervious to hacking attempts, phishing attacks, and ransomware.
That said, cryptocurrency traders need to know the importance of using a secure crypto wallet to avoid being exploited by cybercriminals. Crypto scams are steadily on the rise as revealed by the FBI graph shown in figure 5.
Software engineers building crypto apps should prioritize strong verification. Methods like biometric authentication and decentralized identity (DID), as implemented in our apps, provide a high level of protection against unauthorized access to crypto applications.
Cybersecurity is crucial for the survival of fintech firms today. The digital nature of their processes opens the door to cyberattacks, with new threats constantly cropping up.
As an experienced engineer in the software and IT industry, I urge businesses offering financial services, especially start-ups, to step up their security game.
Adopting best practices like data encryption, multi-factor authentication, and regular security check-ups can help fend off vulnerabilities. Cybercriminals aren’t sitting around, so neither should you.
The company, whose examples and techniques have been highlighted in this article, has worked with numerous businesses to iron out software development challenges, integrating secure coding and real-time monitoring into mobile app development.
A good case study for this service delivery involved helping a client increase operational efficiency and user trust using SDK and API dynamic risk assessment. This approach reduced manual intervention for suspicious activity by 70%, saving significant time for the client's operations team.
In the end, shoring up defenses and staying ahead of evolving threats means that fintech companies can not only protect user trust but also boost innovation without compromising safety.
https://www.statista.com/statistics/1324063/cost-of-data-breaches-in-financial-industry-worldwide/
https://www.kroll.com/-/media/kroll-images/pdfs/data-breach-outlook-2024.pdf
https://krebsonsecurity.com/wp-content/uploads/2024/11/finastra-notice.png
https://www.ftc.gov/enforcement/refunds/equifax-data-breach-settlement
https://www.chainalysis.com/blog/2024-crypto-money-laundering
https://javelinstrategy.com/research/2023-identity-fraud-study-butterfly-effect
https://www.ftc.gov/news-events/topics/protecting-consumer-privacy-security/financial-privacy
https://www.legislation.gov.uk/ukpga/2018/12/contents/enacted
https://www.vistainfosec.com/blog/pci-dss-vs-gdpr/
https://www.techtarget.com/searchsecurity/definition/data-masking
https://www.researchgate.net/figure/MFA-Conceptual-Model_fig1_339076094
On-Chain Media articles are for educational purposes only. We strive to provide accurate and timely information. This information should not be construed as financial advice or an endorsement of any particular cryptocurrency, project, or service. The cryptocurrency market is highly volatile and unpredictable.Before making any investment decisions, you are strongly encouraged to conduct your own independent research and due diligence
Tags :

0 Comments
Show More

Rep. Nick Begich plans to reintroduce a revised Bitcoin reserve bill, renamed the American Reserves Modernization Act, to secure BTC’s role as a U.S. reserve asset.
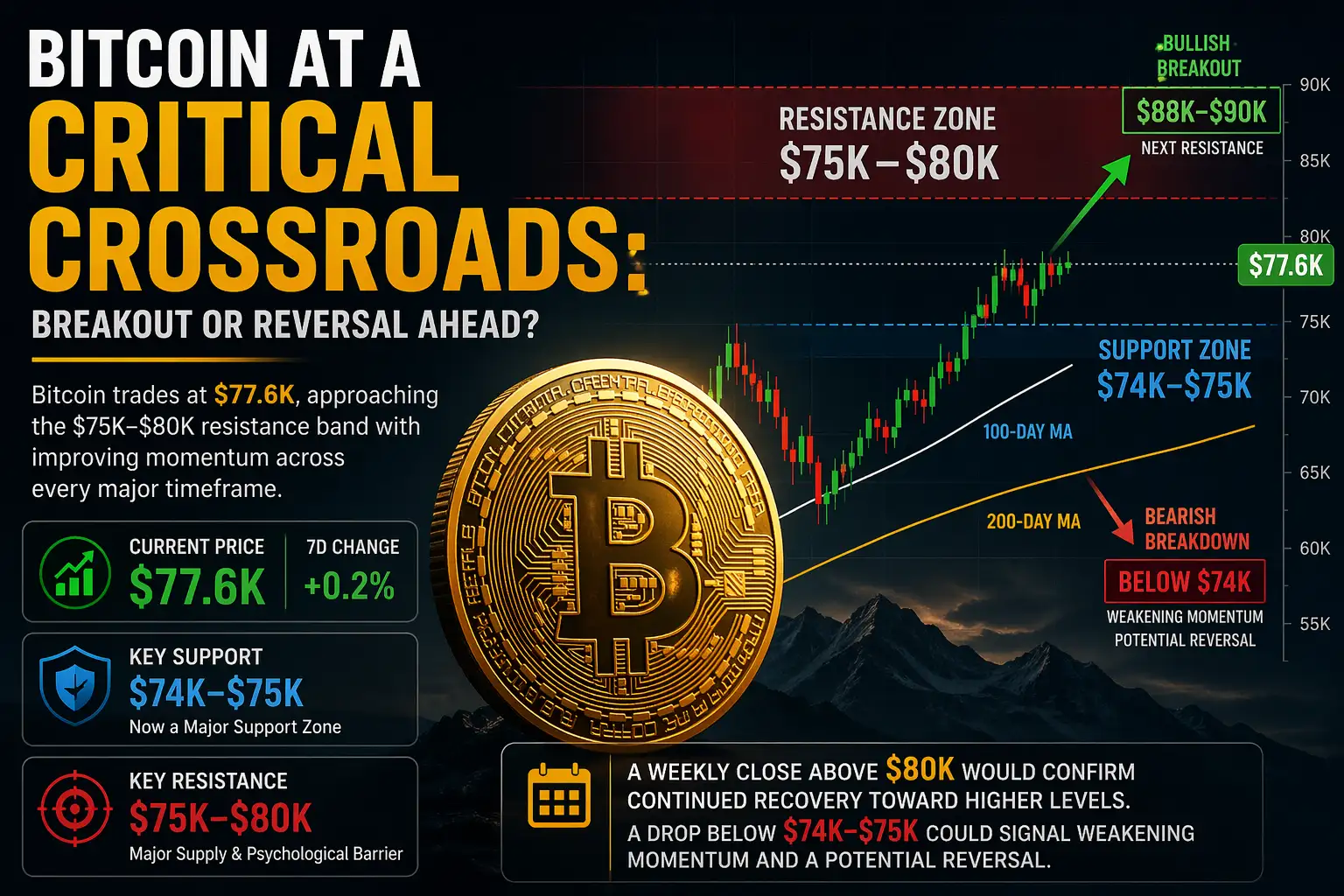
Bitcoin trades near $77.6k as it tests the $80k resistance. Explore On-Chain Media's technical analysis on key support levels and BTC's next major move.

Ditch the Excel sheets. Explore how Web3 careers, from smart contract development to DeFi, offer more freedom, fast growth, and high demand.
On-Chain Media is an independent, reader-funded crypto media platform. Kindly consider supporting us with a donation.
bc1qp0a8vw82cs508agere759ant6xqhcfgcjpyghk
0x18d7C63AAD2679CFb0cfE1d104B7f6Ed00A3A050
CBaXXVX7bdAouqg3PciE4HjUXAhsrnFBHQ2dLcNz5hrM
Contains the last 12 releases